Articles
Tripura: Focusing on IT Enabled Services
Tripura, a landlocked hilly state, bounded on the north, west, south and south-east by Bangladesh and in the east with Assam and Mizoram, has a tropical climate and the main languages spoken are Bengali and kokborok. Rice is the principal crop followed by oilseed, pulses, potato and sugarcane....
Karnataka: Empowering Rural Citizens by Taking ICT to Their Doorsteps
Bridging the gap between the haves and the havenots has been the focus of the Government of Karnataka. The aspiration is being fulfilled by continuously providing more and better services to the citizens. The rural citizens are empowered by taking ICT to their doorsteps thus enabling them...
Karnataka: Empowering Rural Citizens by Taking ICT to Their Doorsteps
Bridging the gap between the haves and the havenots has been the focus of the Government of Karnataka. The aspiration is being fulfilled by continuously providing more and better services to the citizens. The rural citizens are empowered by taking ICT to their doorsteps thus enabling them...
Manipur: Online Tenders for PMGSY through e-Procurement System
Procurement delays, unfair bidding practices, opaqueness in government processes, etc. have become things of the past with the deployment of Government e-Procurement System of NIC (GePNIC) in Manipur. The system provides transparency in the tendering process, reduces time for procurement,...
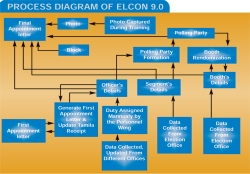
ELECON 9.0: Managing Assembly Elections in Bihar
Polling party formation, deployment of patrolling personnel, tagging of booths with the polling party, Electronic Voting Machines (EVM) randomization, vehicle allotment to the parties - all through random number techniques as per Election Commission of India (ECI) guidelines were made possible...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


