Articles
e-College*Suite: Integrated e-Governance solution for College Campus from NIC
In terms of public governance, India has been a laggard in the utilisation of ICT. There are several reasons for this. One is the monopolistic nature of public governance. It is the customer, in this case the "aam aadmi", who has to like or lump whatever is offered by the public institution....
Introduction of CollabCAD in CBSE Curriculum
Keeping pace with the changing trends and the latest technological development in the field of collaborative design & development of Industrial Designs, CBSE has updated the curriculum for "Engineering Drawing". As a first step in this process the name of the subject has been...
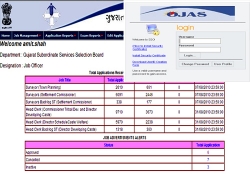
Online Job Application System for Government of Gujarat
Those who are looking for the jobs in Gujarat State government or thinking of making careers along with the various Gujarat Government departments, they can now apply through Online Job Application System.The vision of this online system is to devise an Information and Communication Technology (ICT)...
SMS Application Development using Open Source
SMS - Short Messaging Service has changed the life of the common man, leave alone the benefits of a mobile phone, in staying connected and doing transactions while on the move. SMS integration with e-Governance applications has taken a big leap in reaching the masses renaming SMS as Smart Management...
Commonwealth Express Train - An exposition on wheels
In the past Railways has successfully launched exhibition trains like Azaadi Express, Red Ribbon Express and National Science Express for highlighting Indian Independence, AIDS awareness and Science and Technology respectively. With Commonwealth games being hosted in India, Ministry of Railways...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


