News
IVFRT System launched in Districts of Tamil Nadu
Immigration, Visa, Foreigners registration and Tracking (IVFRT) system was launched for Tamil Nadu districts at Coimbatore on 22nd April 2013. It is a Mission Mode National e-Governance project of Govt. of India to facilitate high level of integrated Visa and Immigration services for foreigners visiting...
Persons with Disabilities (PwD) now able to access information online (http://scpdodisha.nic.in)
Hon’ble Chief Minister, Odisha, Sj. Naveen Patnaik inaugurated the official website of the State Commission for Persons with Disabilities, Odisha on dt-27.04.2013 at 3rd Floor Conference Hall, Odisha Secretariat in a meeting organized by Women and Child Development Department, Govt. of Odisha. ...
Haryana: Requirement Analysis for Integration of Forensic Science Laboratory with existing MedLEaPR System
MedLEaPR (Medico Legal and Postmortem Reporting) system has been developed by NIC Haryana and implemented in Haryana, Punjab and Chandigarh. On 18th March, Hon'ble Punjab and Haryana, High Court, who is monitoring the rollout progress of this system, has approved the new project...
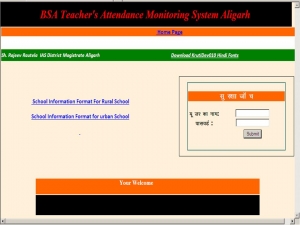
Online System for monitoring Primary Schools in Aligarh, Uttar Pradesh
An online system has been designed and developed by NIC, Aligarh to monitor the prevailing condition of primary schools in the district. The system keeps record of available staff, attendance of students, mid-day meal, uniform distribution, condition of toilets, hygiene, boundary wall, electrical...
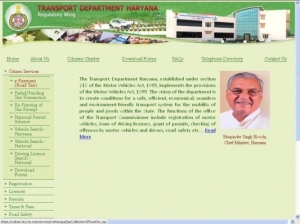
Haryana: Launch of Web portal and SMS services of Transport Department (Regulatory Wing) By Hon'ble Chief Minister, Shri Bhupinder Singh Hooda
Hon’ble Chief Minister, Shri Bhupinder Singh Hooda, launched the web portal (haryanatransport.gov.in) of Haryana Transport Department (Regulatory Wing) on April 10th, 2013 and dedicated it to the citizens of Haryana. The objective is to bring in transparency, facilitate citizens to know...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


