News
NIC Registering Authority Uttar Pradesh
NIC-RA was setup in Uttar Pradesh in the year 2009 with the launch of e-Procurement & e-District system in the state. Various state government departments like PWD, Electronics & IT, Irrigation etc. started using the e-Procurement system which required Digital Signatures as authentication...
State Level Conference on IVFRT in Kerala
Bureau of Immigration (BOI) and National Informatics Centre (NIC) jointly organized the First State Level Conference on Immigration, Visa, Foreigners’ Registration and Tracking (IVFRT) at Sonata Hall, Mascot Hotel, Thiruvananthapuram on 12th March, 2013. About eighty participants from...
Sensitisation programme on e-Auction Process to Bidders & Excise staff of Rayagada Dist. at DRDA Conference Hall on 14/03/13
The “District Level Awareness Programme on e-Auction Process” was conducted on 14-03-2013 at DRDA Conference Hall, Rayagada. The programme was organized jointly by Excise Department and NIC, Rayagada. Shri S. B. Padhi, Collector, Rayagada chaired the programme and Sri Nayak, Excise superintendent,...
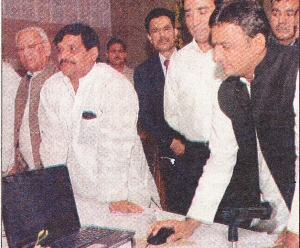
Chief Minister inaugurates the Revenue Court Management System (RCMS) in Uttar Pradesh.
Uttar Pradesh Chief Minister Shri Akhilesh Yadav inaugurated the Revenue Court Management System (RCMS) on 13th March 2013 at Lucknow. He was accompanied by Revenue Minster of UP Shri Ambika Chaudhary, Chairman Board of Revenue Shri Jagan Mathews, Principal Secretary, Department of Revenue,...
Launch of SMART Card based driving license at Mau, Uttar Pradesh
Smart card based driving license (SCDL) system was launched in Mau on 11th March 2013 by District Magistrate Shri Bhupendra S Chaudhary from the Regional Transport Office Mau, Uttar Pradesh. After completing the required formalities, such as bio-metric scanning of fingers and digital photograph...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


