Articles
OJAS (Online Job Application System) - A complete solution for speedy and transparent recruitment process of Government
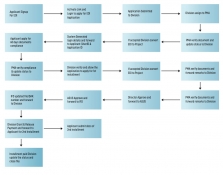
Since inception in 2009, more than 100 departments have been using OJAS platform for their recruitments of various class I, II & III posts. Over 2000 exams have already been conducted using the portal. In 2014, the system was made compulsory by the Government of Gujarat for any type of recruitment....
SAMPADA Suite - Enabling the Food Processing Sector in India
NIC has developed a web based application suite named Sampada Portal (https:// sampada-mofpi.gov.in) for various schemes under which the Ministry provides grants to various promoters desirous of setting up Food Processing Facilities.
e-Labharthi - Heralding a new approach towards electronic service delivery with a Common Social Registry of Beneficiaries for DBT
Students, farmers, pensioners, disabled, poor, and vulnerable sections of the society comprising the bulk beneficiaries of the various schemes of the government of Bihar had a pleasant surprise when they swiftly and securely received their share of fund benefit directly into their bank...
Digital Village Harisal - Striding with the Digital Way of Tribal Development
Technology enablement activities took a big leap at Harisal village from March 2016. Since then, several organizations have partnered in initiatives to address gaps in the progressive path. Many more joined the path of transformation from mere digital technologies to smart technologies....
Tirunelveli District - Where District Administration is Reinforced by ICT Tools
Tirunelveli District is one of the oldest districts in Tamil Nadu which is always prominent for its richness in Administration. It is also named Oxford of South India due to its large number of educational institutions. Though the District Administration is always succeeding in a traditional...




 Subscribe
Subscribe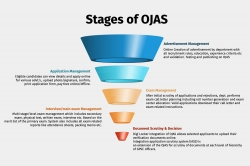




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

