Articles
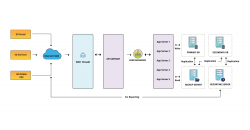
BYOB- Build Your Own Bot - BYOB + VANI = Single window destination for Bot lifecycle
As was mentioned by multiple speakers in RAISE2020, BYOB aims to democratize AI beyond the realms of technical personnel. BYOB aims to empower change-makers in the government domain like Mr. Ranjitsinh Disale (Global Teacher Award Winner 2020), a simple school teacher, who used technology...
Online Booking System of BCD - ICT-driven Solution for Building Construction Department, Bihar
After a year of implementation of these digitization processes, the Building Construction Department, Govt. of Bihar was able to approve around 240 booking of Bhawan and after implementation, during 2018- 2019, 2019-2020 revenue of Rs. 4.96 Crore and Rs. 5.48 Crore was generated respectively through...
Integrated ShalaDarpan - Decision Support System for Schools Monitoring & Management
ShalaDarpan is a unique idea to provide an end-to-end solution to the Education department for effective monitoring and management of all Government Schools. System facilitates decision support, Planning (School Open/ Upgrade/ Merge/ Close), School operations (Admissions, Promotions,...
Patna District - Combating Covid-19 pandemic situations with efficient ICT interventions and Management
Patna became the first district to implement the e-Pass system of NIC in Bihar. With the application, a web portal was also created to enable citizens apply for e-Pass with much ease. The system has benefitted many who were stranded due to medical or other emergency reasons at various...
Akola District - Pioneer with excellence in digital governance at the Cotton City of India
NIC, Akola is a pioneer with excellence in digital governance, with communication facilitation, technical support, system analysis, and innovative implementation of ICT. NIC, Akola is recognized with more than twenty various types of awards and recognitions for innovative initiatives...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

