Articles
Certificate Generation Module - Using Service Plus framework
A Certificate generation module was considered prudent to be developed where Gram Panchayat, Panchayat Samiti and Block Level Officials can process the service requests of citizen and deliver online certificates in an organized manner. Common services required by citizen include income...
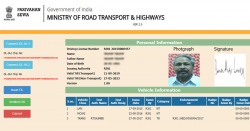
Online Key Management System - for Driving License and Vehicle Registration
A web-based KMS system was considered prudent to be developed for the implementation of specifications notified by the Transport ministry as per gazette notification of 1st March 2019 for Smart card based DL and RC. The new webbased KMS system is designed, developed, and implemented by...
Kozhikode District - effective citizen centric governance through citizen participation
Kozhikode district played a key role during the Covid 19 pandemic not only in the district but also in the entire state of Kerala by providing real-time surveillance and health monitoring solution Covid19jagratha. Nammude Kozhikode Mobile App is a Technology Platform to facilitate...
Hisar District - Signature of excellence in Innovative ICT at grass-root Informatics
NIC District Centre, Hisar has been extending its ICT enabled support and services to the District Administration and various departments of the State Government and Central Governments by commissioning State-of-the-art infrastructural including three Video Conferencing studios, IT...
Shimla District - The Queen of Hills Going Digital
District Shimla has tough terrain and most of the area is snowbound, the automation and computerization activities are tough to implement in farflung areas of the District. The citizen service centres named SUGAM have been set up in the lower offices up to Sub Divison and Tehsils. One...




 Subscribe
Subscribe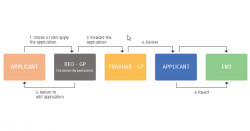




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

