News
Haryana - One day workshop on Court Cases Monitoring System (CCMS) Organized
The Court Cases Monitoring System (CCMS) Web based software, developed & hosted by NIC Haryana, is being implemented by most of the departments & PSUs of Haryana. The CCMS is a web based centralized solution having features like: Centralized data input &...
The new Prime Minister of India's website launched by NIC
Just in seconds after Shri Narendra Modi was sworn-in as the 15thPrime Minister of India, the official website of the Prime Minister of India was made live by the NIC’s web development team with active coordination from NIC Cell at PMO. Office of the Prime Minister and IT official...
Two days state level workshop on CFORM and SFORM at Aizawl, Mizoram
NIC Mizoram in association with State Home Department, Mizoram have organized a two days workshop cum hands-on training program on CFORM and SFORM online application at Mizoram state. The workshop was held at Secretariat Conference Hall, New Secretariat Complex, Aizawl on 22nd and 23rd of May, 2014. ...
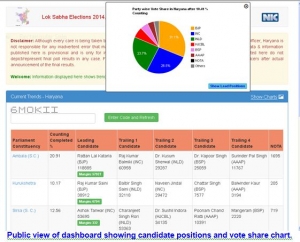
Haryana: Lok Sabha Elections-2014 - E-Dashboard for counting implemented (16th May,2014)
A web based E-Dashboard for Counting of votes has been developed at NIC Haryana in Coordination with the office of Chief Electoral Officer, Haryana. This dashboard was implemented on 16/05/2014 during the counting of votes for Lok Sabha elections 2014. The Dashboard is web based dashboard...
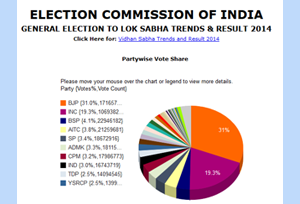
Results of General Elections to Lok Sabha 2014
Since Independence, free and fair elections to the largest democracy of the world – INDIA, are being held at regular intervals as per the principles of the Constitution, Electoral Laws and System. Section 14 of the Representation of the People Act, 1951 provides for conduct of the elections...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


