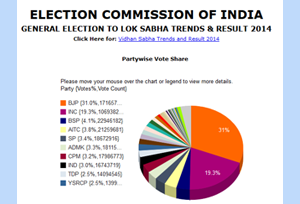
Results of General Elections to Lok Sabha 2014
Since Independence, free and fair elections to the largest democracy of the world – INDIA, are being held at regular intervals as per the principles of the Constitution, Electoral Laws and System. Section 14 of the Representation of the People Act, 1951 provides for conduct of the elections to constitute a new Lok Sabha before the expiry of current term.
After taking into account the Constitutional and legal provisions, the Election Commission of India made comprehensive preparations for conduct of elections to the 16th Lok Sabha. It was decided that the General Election to the House of People, 2014 to constitute the 16th Lok Sabha shall be held as per schedule finalized for General Elections to be held on 9 poll days.
The Election Commission is responsible for planning and executing a whole amount of complex operations that go into the conduct of elections. Since free, fair, fearless and participative election involves complex planning, detailed analysis and series of consultations with all stakeholders Election Commission evolved a detailed framework for smooth delivery of General Elections.
Election Commission of India requested NIC to provide technical support for dissemination of Election results and trends to be disseminated on 16/05/2014 from 8:00 AM onwards. NIC prepared the infrastructure at two data centres as follows:
- NDC, Shastri Park (Primary for countingservice.nic.in, eci-countingservicepc.nic.in, eciresults.nic.in)
- NDC, Hyderabad (Primary for eciresults.ap.nic.in and DR for countingservice.nic.in and eci-countingservicepc.nic.in)
The results delivery architecture was designed in High Availability (HA) mode keeping in view of the high computational requirements. The results were made available at http://eciresults.nic.in/ and http://eciresults.ap.nic.in/.
Expecting large number of hits from across the world, CDN technology was used for smooth delivery of election results. Total of 467 million hits were recorded with peak of 13357 hits/ second. The results dissemination process was a great success without any technological glitches in spite of such high demand on the infrastructure resources.
ECI team and NIC team worked in close collaboration to ensure smooth delivery of the election results, thus setting a benchmark for successful delivery of services of this magnitude.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


