Haryana: Lok Sabha Elections-2014 - E-Dashboard for counting implemented (16th May,2014)
A web based E-Dashboard for Counting of votes has been developed at NIC Haryana in Coordination with the office of Chief Electoral Officer, Haryana.
This dashboard was implemented on 16/05/2014 during the counting of votes for Lok Sabha elections 2014.
The Dashboard is web based dashboard which has three separate modules:
1. Admin module for data entry from counting centers.
2. Monitoring module for the CEO and Returning Officers.
3. Public View.
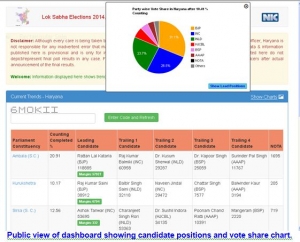
The data on dashboard was populated by 90 users from over 30 counting locations. The dashboard helped the, Returning officers to monitor round wise date entry by 90 ARO (Assembly segment wise). The CEO could monitor the counting progress for whole Haryana and the public view provided graphical details of counting progress, party positions and lead margins of various candidates.
The dashboard is hosted at http://electharyana.nic.in.
The public view software has the features to show candidate wise votes polled in Parliamentary constituency, the leading candidates along with lead margin, four trailing candidates and NOTA votes. It also depicts the progress of counting i.e. % of counting completed in each segment, a bar chart depicting the party positions and a pie chart showing vote share of various political parties in whole state as well as in each PC.
The RO module of the dashboard has the features to enter round 0 votes (i.e. postal ballots), monitor the round wise progress of each assembly under that PC and Finalization of results by RO.
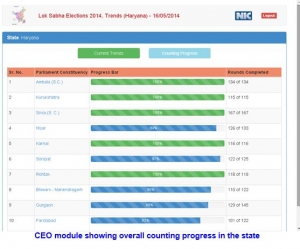
The CEO module has the features to monitor over all counting progress in whole state and detailed monitoring of round wise progress each assembly segment of the state.
CEO,Haryana, ROs, DEOs, AROs & other authorities continuously monitored the result trends till results were finally declared. A media centre was setup in CEO office and all RO offices where the result trends were showcased to media using NIC Haryana Counting Dash Board software.
NIC Haryana had setup special infrastructure for the counting day which included:
1. Two high end web servers (IIS 7.5) in load balancing mode for public view.
2. One high end web server for data entry from counting centers (This web server was accessible to CEO, ROs and AROs only). 3. One SQL Server 2012 Database Server with 164 GB RAM as backend database server.
The CEO, Haryana appreciated the efforts of NIC Haryana gave a press briefing regarding counting Dashboard to the various News representatives.
Hit Statistics for Counting Monitoring dashboard, Haryana (http://electharyana.nic.in).
Total Site Visits: 14, 20,144
The dashboard was made mobile compatible also which enabled users to view the dashboard on wide variety of devices including mobile devices.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


