News
Training on Bhunaksha held at Jharsuguda, Odisha
Training programme on Bhunaksha software on map correction was held in the DRDA Conference hall, Jharsuguda, Odisha on 09/08/2017 for all the 5 Tahasil officials and 32 RI officials of Jharsuguda District. The training programme was organized by NIC, District, Unit, Jharsuguda. The main objective...
Visit of Smt. Neeta Verma, Director General, NIC to NIC Odisha State Centre, Bhubaneswar
Director General, NIC, Smt. Neeta Verma accompanied by Shri S S Gahlout, DDG & Head (Infra.) visited NIC Odisha State Centre, Bhubaneswar on 2nd August 2017. Government of Odisha declared Madam as State Guest and accorded befitting hospitality. DG, NIC was greeted by Shri P. K....
Roll out of online mutation (LRMS) system at Kendrapara Tahasil, Odisha
The Land Records Management System, a web enabled application for online mutation, was launched at Kendrapara Tahasil recently. It is a transaction based applications which interacts with the e-Registration application through web services. It helps the Mutation Officer (Tehsildar/Addl....
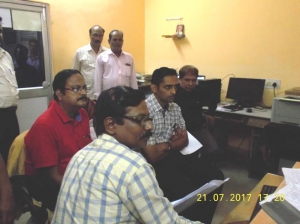
Training on BHUNAKSHA 3.0 at NIC Balangir District, Odisha
Training on Bhunaksha was organised at NIC, Balangir for all 14 Tahasils of Balangir District, Sub-division wise. The schedule was as follows: 05.07.2017 & 06.07.2017 - Balangir Sub-Division (6 Tahasils) 13.07.2017 & 14.07.2017 - ...
Inauguration of Video Conferencing Facility at Nyaya Sanjog, Odisha State Legal Services Authority
Hon'ble Shri Justice Dipak Misra, Judge, Supreme Court of India & Executive Chairman, NALSA inaugurated VC facility at the Legal Assistance Establishment (Nyaya Sanjog) set up in the office of the Odisha State Legal Services Authority(OSLSA), Cuttack in presence of Hon'ble Chief...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


