Automation
BALANGIR -IN QUEST OF EXCELLENCE
Balangir district, the cultural hub of Western Orissa, is spread over a total geographical area of 6569 sq. km. Comprising mostly of tribal inhabitants. Balangir district encompasses a population of 13,37,194 as per the census data of 2001 in 6 tehsils, 14 blocks and 1794 villages. The district bears...
West Kameng: Building Confidence towards ICT Enabled Services
Located in a mountainous tract with altitude varying from 650 ft to 13714 ft - West Kameng District of Arunachal Pradesh derives its name from the Kameng river, a tributary of the mighty Brahmaputra that flows through the District. The district comprises five major tribes: Monpa (which makes up 78% of...
Minerals Activities Administration System in Karnataka
Department of Mines and Geology (DMG), Government of Karnataka is the nodal government department administrating the mining and mineral development activities in the state. Department of Mines and Geology (DMG), Government of Karnataka is the nodal government department administrating the mining and...
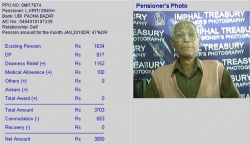
Pension Payment System: G2C Services in Manipur
The government expenditure towards payment of pension in Manipur constitutes a major component of annual Non-Plan expenditure. The manual system of pension payment suffered from several procedural gaps resulting in forged Pension Payment Order (PPO), impersonation, miscalculation, over payment, non-recovery...
West Bengal: Transforming With Widespread Adoption of ICT
West Bengal - a leading state in Eastern India, famous worldwide for Darjeeling Tea produced in the northern hill region and Royal Bengal tigers found in the Sunderbans on its southern part forming the worlds largest delta by the mighty rivers Ganges, Brahmaputra and Meghna.West Bengal can boast of...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


