Automation
Medical Seat Allotment through Video Conferencing
In order to promote the excellence of Medical education in the country and to bring in transparency, Ministry of Health & Family Welfare, Govt. of India, had evolved a scheme for systematizing the prospective intake of students for both undergraduate and postgraduate medical courses in 1993, after...
NIC is our Partner for e-governance Since the Creation of the State
Shri Jyoti Bhramar Tubid, a 1983 batch IAS officer of the state and posted as Principal Secretary, Department of Home, Govt. of Jharkhand. In an interview with us he reveals his views and plans about ICT specifically for the Department of Home & Police and in general about the present e-governance...
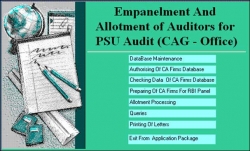
ICT initiative in Empanelment of CA Firms for Allotment of PSU Audit
The Comptroller & Auditor General (CAG) Of India as the Head of Supreme Audit Institution of India conducts the auditing of accounts of all the government organizations and companies in which government interests are involved. The government offices are audited by its field offices, spread across...
Manipur: Adding another jewel through ICT based e-Governance
Manipur is a state in NE India which is surrounded by hills on all the sides and decorated by innumerable beautiful flora and attractive fauna. It is made more enchanting with its unique natural setting, comprising of eye-catching waterfalls, lakes, streams and evergreen forests. Although a tiny state,...
State in Focus Maharashtra: Connecting People and Government
The word Maharashtra, the land of the Marathi speaking people, appears to be derived from Maharashtri, an old form of Prakrit. Located in the north centre of Peninsular India, with a command of the Arabian Sea through its port of Mumbai, Maharashtra has a remarkable physical homogeneity, enforced by...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


