Automation
Self Healing Software System to Fix Post Release Errors
Availability & Reliability are the two critical terms used basically to describe the robustness of any software system but these two parameters are affected mostly by post released errors. The biggest loophole in current system is the lack of adequate intelligence in the software to response reactively...
Amravati: Using ICT to Reach the Poor Directly
Amravati is also known as Amrawati or Amraoti. It is believed to be the city of Lord Indra, the king of gods. The city boasts of historical temples of goddess Amba, Lord Shri Krishna and Shri Venkateshwara. But today the district is known for its robust ICT implementations, advanced communication technologies...
Dholpur: ICT Shines on the Eastern Gateway of Rajasthan
Situated in the eastern part of Rajasthan bordering Uttar Pradesh and Madhya Pradesh, Dholpur earlier called Dhavalpur, was carved out of Bharatpur in 1982. It is famous for its sandstone and ravines which are part of Chambal legacy. The famous Dholpur House (UPSC HQ), President House and...
OCMMS for State Pollution Control Board
Online Consent Management & Monitoring System for State Pollution Control Board (OCMMS) is web based Generic Model for implementing a well-coordinated system applicable to most SPCBs and PCCs. This system allows industries for the online submission of application for CTE/CTO & for various categories...
IntraGov Haryana:Facilitating Core Government Functions
The IntraGov-Haryana is aimed to provide a single point gateway which integrates government transactions and services within Civil Secretariat as well as those between Chief Secretary Office and Secretariat employees. The IntraGov Haryana has been developed & implemented as an Intra Government Transactions...




 Subscribe
Subscribe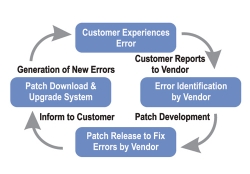





 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

