Automation
Online Job Application System for Government of Gujarat
Those who are looking for the jobs in Gujarat State government or thinking of making careers along with the various Gujarat Government departments, they can now apply through Online Job Application System.The vision of this online system is to devise an Information and Communication Technology (ICT)...
Introduction of CollabCAD in CBSE Curriculum
Keeping pace with the changing trends and the latest technological development in the field of collaborative design & development of Industrial Designs, CBSE has updated the curriculum for "Engineering Drawing". As a first step in this process the name of the subject has been...
Pregnancy, Child Tracking and Health Services Management System
NIC Rajasthan has developed and implemented the Pregnancy, Child Tracking & Health Services Management System (PCTS) for Medical, Health & Family Welfare Department, Govt. of Rajasthan, for improving its services right up to the grass root level (Health Sub centre). It is online...
Jammu & Kashmir: Embraces ICT for e-Governance
J&K State comprises of three geographical regions, namely Jammu, the Kashmir valley and Ladakh. Administratively, it is divided into two divisions namely Jammu and Kashmir. Jammu is the winter capital and Srinagar is the summer capital. J&K has 22 Districts of which 8 are newly created....
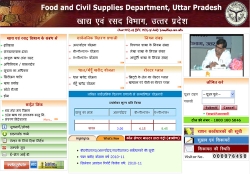
Uttar Pradesh:Focusing on Rural e-Governance
Uttar Pradesh is the most populous state accounting for about 17 percent of the country's population. It is the fourth largest state in terms of size covering nearly 9 percent of the country's geographical area. With 72 districts and nearly 1 lakh villages the state is also larger...




 Subscribe
Subscribe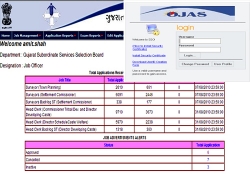



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


