Technology
Digital Signature Certificate Workshop Organised at Shimla
A workshop on the Digital Signature Certificates was organised at Shimla on 14th July 2014 for the Heads of Departments and other officials of the State Government. The faculty for the workshop was provided by the Controller of Certifying Authority (CCA) Government of India. More than fifty senior...
Two Days Training Workshop on State e-PMS Portal conducted for Karnataka on 4th-5th July 2014
“ePMS, an On-line Project Management System for Karnataka tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire...
Two Days Training Workshop on State e-PMS Portal conducted for Assam on 7th-8th July 2014
“ePMS, an On-line Project Management System for Assam tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire tracking...
The new Prime Minister of India's website launched by NIC
Just in seconds after Shri Narendra Modi was sworn-in as the 15thPrime Minister of India, the official website of the Prime Minister of India was made live by the NIC’s web development team with active coordination from NIC Cell at PMO. Office of the Prime Minister and IT official...
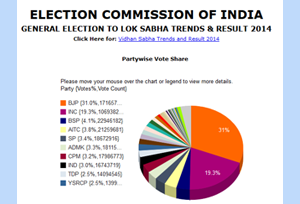
Results of General Elections to Lok Sabha 2014
Since Independence, free and fair elections to the largest democracy of the world – INDIA, are being held at regular intervals as per the principles of the Constitution, Electoral Laws and System. Section 14 of the Representation of the People Act, 1951 provides for conduct of the elections...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


