Technology
CPCB-eSamikSha online system for monitoring and compliance mechanism launched by Shri Anil Madhav Dave Honourable Environment Minister, on 23rd Nov, 2016.
Shri Anil Madhav Dave, Minister of State (Independent Charge) of Environment, Forest and Climate Change (MoEF&CC), launched the CPCB-eSamikSha Portal on 23rd November, 2016 in the 61st Conference of Chairmen & Member Secretaries of Pollution Control Boards and Pollution Control Committees...
Mobile App Launched at Indira Gandhi Krishi Vishwavidyalaya, Raipur, Chhattisgarh
On the 20th Jan’2016, the 30th foundation day of the Indira Gandhi Krishi Vishwavidyalaya (IGKV), Raipur the National Workshop on “Concepts of Higher Education and its Future Nature” was organized. On this occasion the university moved one step ahead towards ICT penetration...
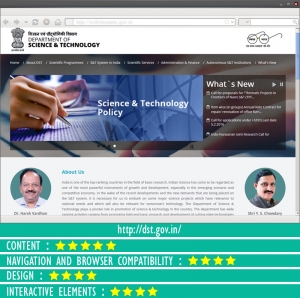
Department of Science and Technology
The Department of Science & Technology plays a pivotal role in promotion of science & technology in the country. The department has wide ranging activities from promoting high end basic research and development of cutting edge technologies on one hand to provide service to the technological...
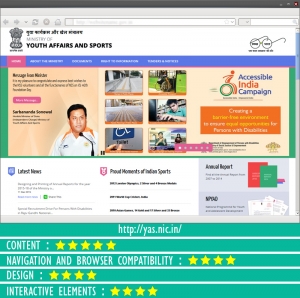
Ministry of Youth Affairs and Sports
The Ministry of Youth Affairs & Sports was initially set up as the Department of Sports in 1982 at the time of organization of the IX Asian Games in New Delhi. Its name was changed to the Department of Youth affairs & sports during celebration of the International Youth Year, 1985. It became...
eSamikSha did great job in Nepal Mission Success
eSamikSha played a seminal role in India’s gigantic rescue and relief mission in Nepal and India after the April 25 earthquake, which has been a big success by all accounts. The rescue and relief operation in the aftermath of the devastating earthquake was incessantly monitored at the highest...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


