Trainings
Chhattisgarh Leads Digital Push for Road Safety at DRM Meet on eDAR Project
The District Road Managers (DRM) meeting on the eDAR project concluded successfully today, with State Informatics Officer Shri T. N. Singh praising the team's dedication and offering key guidance. The session drew senior officials including Shri Arvind Yadav (Director IT), Shri Aninda Paul...
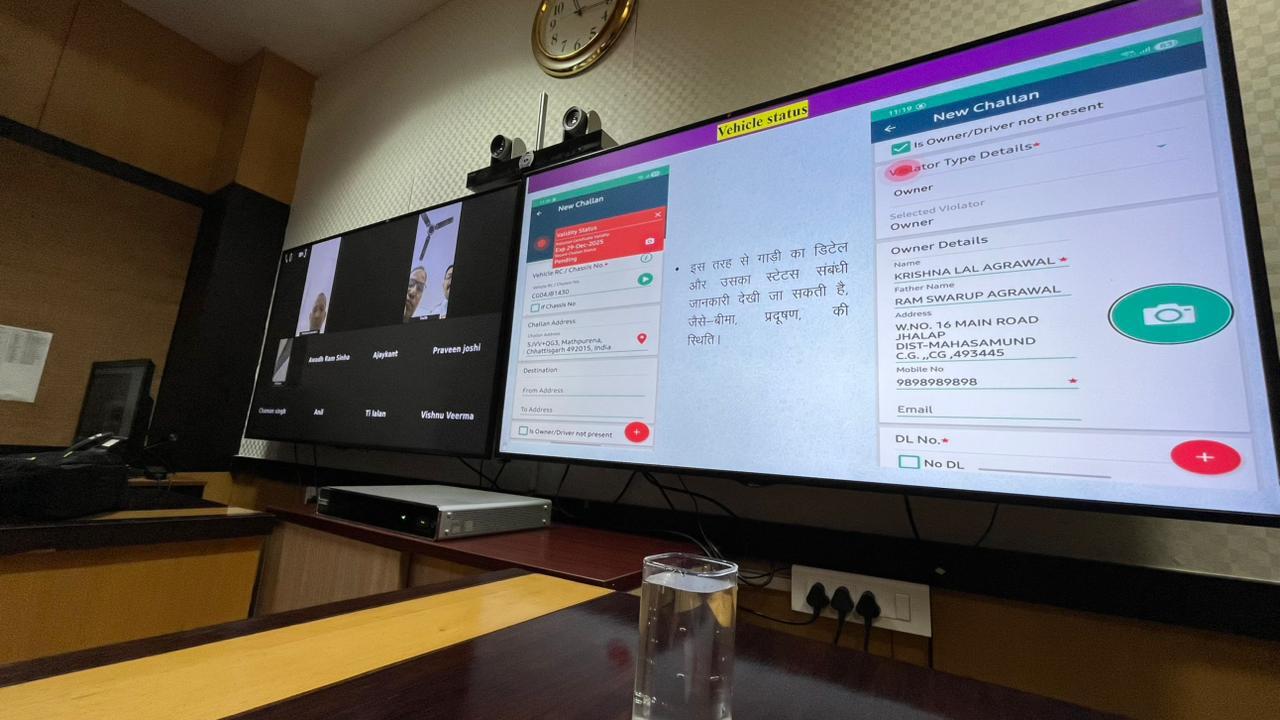
Training on eChallan System Held at Mahanadi Bhawan
A comprehensive training session on the eChallan system was successfully conducted on 20 February 2026 at Mahanadi Bhawan, Mantralaya, bringing together more than 100 officials from the Transport and Traffic Departments. The session was led by Arvind Yadav, Director (IT), and Amit Kumar Dewangan,...
NIC, Odisha observed Safer Internet Day across the State
With the digital landscape evolving rapidly through the rise of artificial intelligence, the Odisha Unit of the National Informatics Centre (NIC) spearheaded a massive awareness campaign to mark Safer Internet Day 2026. Observed annually on the second Tuesday of February, this global initiative serves...
Training Programmes Conducted under Road Safety Month 2026
Under Road Safety Month 2026, comprehensive training programmes were organized by the District Rollout Managers for the effective implementation of the eDAR project in the districts of Balod, Bemetara, Mungeli, Janjgir, Rajnandgaon, and Kanker in Chhattisgarh. In recognition of their exemplary...
Training Programme on e-Uttar Portal Organized
Raipur, 11 February 2026: A special training programme was organized today at the S-5 Auditorium, Mantralaya (Mahanadi Bhawan), Atal Nagar, Nava Raipur, with the objective of ensuring the smooth and fully digital conduct of the upcoming Budget Session (February–March 2026) of the Sixth Legislative...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


