Articles
Mid Day Meal Automated Reporting & Management System (MDM ARMS)
The Mid Day Meal Scheme is one of the most well-known schemes initiated by the Government of India. NIC, Himachal Pradesh has taken the initiative to push the effciency of the scheme to the next level using ICT by creating the MDM-ARMS software and a related mobile based App to improve the management...
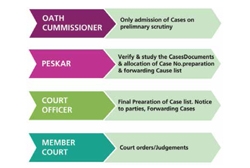
Revenue Court- Case Monitoring System of Odisha
Petitioners can now register a case online and track its status. Cause list is generated dynamically, which is published on the portal after approval by the competent authority. Hearing Notice is served online to the petitioner/ advocate and opponents by way of SMS, e-mail and physically through the...
Oral Pre-Cancer Mobile App
The innovative App is very useful for Doctors and Dental Assistants in the diagnosis process and management of oral cancer in its early stages. ICT thus helps improve the quality of life of the citizens and saving lives using the best that ICT has to offer.
Online Consent Management and Monitoring System of JSPCB
Jharkhand State Pollution Control Board (JSPCB) has taken various initiatives during past year and a half, with the objective of 'Ease of Doing Business' in the State for transparent and expeditious decision making.
Telangana's Rashtriya Bal Swasthya Karyakram Software
This software captures various health conditions of children in the target age group. In cases where diseases are detected, or if medical intervention is required, support is provided free of cost and the parents of the affected children are informed through SMS automatically.




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


