Articles
District Namchi, Sikkim
NIC South District Unit of Namchi was established in the year 1993 and since then had a key role in promoting e-Governance in the District using Information and Communication Technology. Many software applications, websites and mobile apps have been developed and implemented with an objective to bring...
District Bhojpur, Bihar
District Bhojpur has been striding ahead in a progressive path of e-Governance since 1988 with the establishment of NIC Unit in the district. NIC continues to be instrumental in successfully implementing several ICT based initiatives. The achievements story continues.
Power Usage Efficiency In West Bengal State Data Centre
Data Centres consume a considerable amount of power for their smooth functioning and can cause significant loss of money and energy with lack of proper infrastructure management. Findings and strategies contextual to West Bengal State Data Centre for optimizing the utilization of power energy resources...
Combating RANSOMWARE
Ransomware is a threat to Netizens, one that has become increasingly popular with criminals in the recent past. Combating this challenge requires not only the development of new technologies but also good Internet practices on the part of the users.
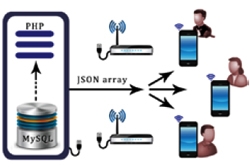
Case Hearing Status (CHS) Mobile App
The Android based CHS mobile App developed by NIC's Unit at Andaman & Nicobar is a modern and easy facilitation to access the daily cause list put up for case hearing procedure of the District and Sessions Courts of Port Blair. Now, the real time case progress status can be viewed through mobile...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


