Articles
Centralized Antivirus Management
In order to have a centrally managed antivirus solution for NICNET, National Informatics Centre has deployed three-tier architecture for Antivirus management. One Antivirus Distribution/ Relay Server is deployed at each Bhawan/State and a Central Antivirus Server is installed at NIC (HQ).
Dark Net - The Hidden Side Of Web
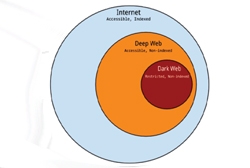
Dark Net is a specific part of the hidden Web where one can operate in total anonymity. It isn't illegal to browse the dark web in most countries, but using some of the dark web services can be illegal. Access of dark web is a little like stepping back in time to the early days of the internet...
District Sirmaur - Committed Towards Digital India
Winning the top award during the Digital India Week celebration 2015 underlines NIC Sirmaur's true commitment towards making the dream of Hon'ble Prime Minister to transform India into a digitally empowered society and knowledge economy.
District Patna - Fostering ICT For e-Governance With Mobile Applications
Set up in the year 1988, NIC District unit of Patna has been playing a key role in computerization, providing efficient software solutions and carrying out various ICT activities for this glorious city. Several mobile applications have been introduced to enable good e-Governance in the District.
ICT Shines in the Sun City
Jodhpur Development Authority (JDA) was established with the objective of providing basic infrastructure in Jodhpur district to meet the ever- growing demand of public and carry out continuous improvement in the city. NIC Jodhpur Centre is providing remarkable ICT support and services to the Authority...




 Subscribe
Subscribe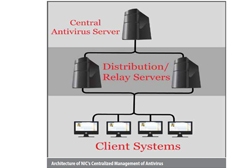




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


