Articles
National eGov App Store: Reusable Application Availability Store
Application stores are ideal solutions for hosting applications and components that can be re-used by other departments at the Centre and the States without investing cost and efforts in development of the same. As a precursor for realizing the importance of application stores, NIC developed...
Biometric Attendance System (BAS) - National Rollout
Digital India programme of Government of India seeks to transform India into a digitally empowered society and knowledge economy. As a part and parcel of this programme, DeitY/NIC/ UIDAI has implemented Aadhaar enabled Biometric Attendance System (BAS) in all the Central Government Offices...
Bhagalpur : e-Governance in the Silk City of Bihar
Bhagalpur, situated on the southern banks of the holy River Ganga, is famous for producing Tassar silk and sarees and hence also known as the Silk city of Bihar. The important places to visit are the ancient Buddhist University at Vikramshila, Jain Temple at Nathnagar, Sahjangi and the Ajagaibinatha...
JHARSUGUDA: Revolutionizing Governance through ICT
Jharsuguda - one of the most industrially developed districts in the state of Odisha, is situated at a distance of 372 km from the state capital Bhubaneswar. It was created on 1st April, 1994 bifurcating Sambalpur district. It covers an area of 2, 081 sq. km. and lies between 21.82 degree north...
UDAIPUR: ICT Cruise at The City Of Lakes
Udaipur, the capital of the former princely state of Mewar, is a serene city located in Rajasthan and is famous world over for its lakes. Also known as the City of Lakes, Udaipur is one among the most romantic and beautiful cities of India.




 Subscribe
Subscribe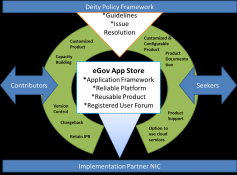





 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

