Articles
Faridabad: ICT in the Medical & Educational Hub of Haryana
Faridabad was founded in 1607 A.D. by Shaikh Farid, the treasurer of Jahangir, with the objective of protecting the highway which passed through the town. It came on the map of Haryana on 15th August, 1979 as the 12th district of the state. Situated about 25 Kms. from Delhi, it is a part of...
KULLU: Leveraging ICT in Dev Bhoomi
Kullu, known as the Valley of Gods and Apples, derives its name from the word KALUT which was a tribe in the upper valley of River Beas. It is famous for International Folk Dance festival and Kullu Dussehra. The district comprises of 4 Sub-Divisions, 7 Tehsils, 2 Municipal Corporations, 3...
e-Quarters System : A Unique G2E Web Enabled Platform
With the objective to introduce transparency and to improve the system of allotment of G.A. Pool Quarters, based on eligibility and choices exercised by the applicants, an Automated e-Quarters System has been introduced.
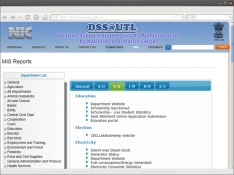
NIC-eDSS: Decision Support System of Lakshadweep Administration
Decision Support Systems (DSS) are interactive, computerbased systems that aid users in judgment and choice activities. They provide data storage and retrieval along with enhancing the traditional information access and retrieval functions with support for model building and model-based reasoning. They...
ICT Initiatives in the Office of Chief Secretary, Haryana
The Chief Secretary Office (CSO) is the Principal Executive Office of the Government of Haryana. The Chief Secretary Haryana also holds the charge of General Administration, Personnel, Training, Vigilance, and Administrative Reforms Departments. The CSO monitors and coordinates the work pertaining...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


