Networking
Durg District Leads in Implementation of MedLEaPR Platform
Durg district has taken a major step in modernizing medico-legal documentation by successfully implementing the MedLEaPR (Medico-Legal Examination and Post-Mortem Reporting) platform. With this, Durg has become one of the leading districts in Chhattisgarh to digitize medico-legal reports and ensure...
Seminar on latest technology in terms of Networking & Data Centre Architecture
A seminar on “Latest technology in terms of Networking & Data Centre Architecture” was organised at the VCR Hall of NIC, Bhubaneswar on 22nd June 2017 in coordination with Cisco Systems, Inc. Shri P. K. Pramanik, DDG & SIO initiated the seminar with introductory address on...
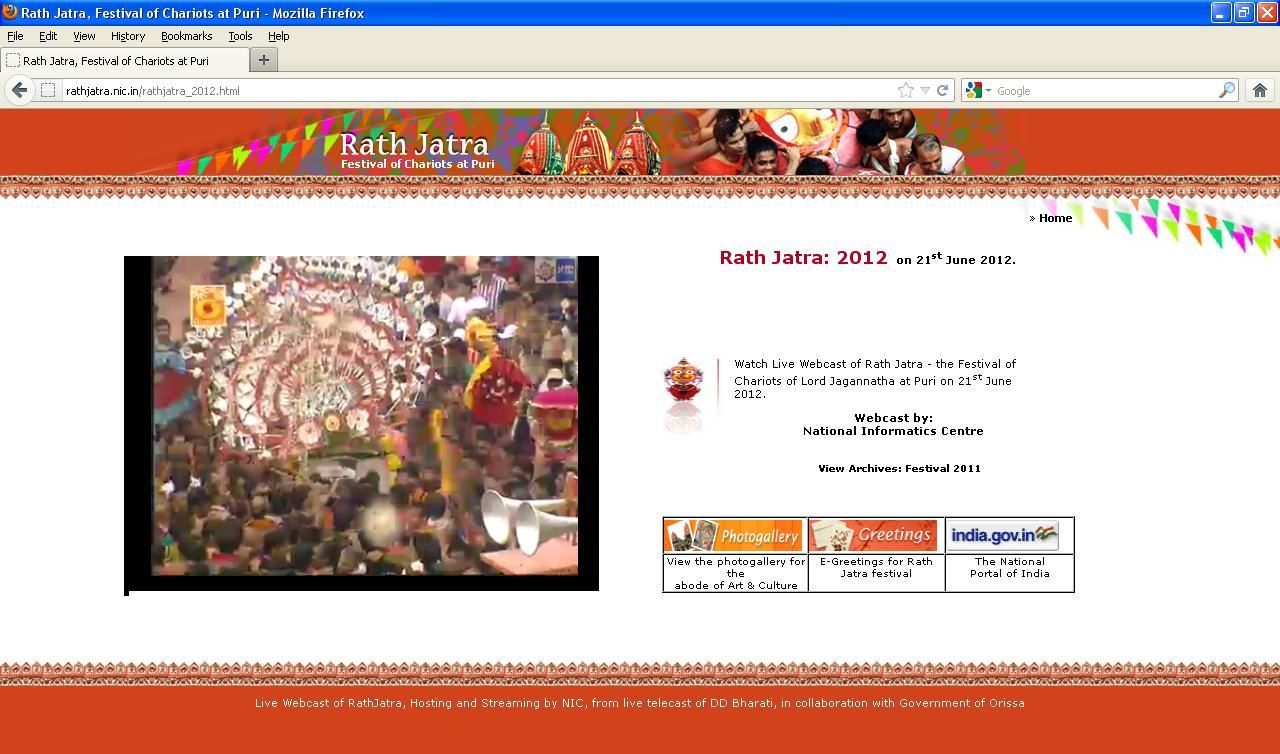
Rath Jatra - 2012 on Live Web Cast
The much awaited Car Festival -2012, the festival of chariot of Lord Jagannath, Puri has taken place this year on 21st June 2012 followed by Bahuda Jatra on 29th June and SunaVesa on 30th June 2012. National Informatics Center(NIC), Odisha State centre did live webcast of the mega festival...
Haryana: Live web cast of 47-Adampur Booths and other ICT value addition support To Election process by NIC-Hisar
Today (30th November 2011) one can enjoy the live web casting and other value addition as mention here. NIC District Unit, Hisar has developed a dedicated and comprehensive web site for facilitating to the voters, citizen and the officers involved in conductions of election. Following web sites...
A State-wide Review-cum-Orientation Programme through VC on MCTS Application in the state of Orissa on 24th May 2011
A State Level Review-cum-Orientation Programme on MCTS (Mother and Child Tracking System); a system of name-based tracking of pregnant mothers and children for better coverage of ANC, institutional delivery and immunization; was organized through multipoint-VC on 24th May 2011 in which all the 30...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


