Articles
ICT Initiatives in the Office of Chief Secretary, Haryana
The Chief Secretary Office (CSO) is the Principal Executive Office of the Government of Haryana. The Chief Secretary Haryana also holds the charge of General Administration, Personnel, Training, Vigilance, and Administrative Reforms Departments. The CSO monitors and coordinates the work pertaining...
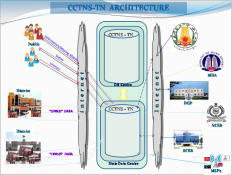
Implementation of CCTNS Project in Tamil Nadu
The ambitious Crime and Criminals Tracking Network & System (CCTNS) project was conceived as one of the 31 Mission Mode Projects of Indias National e-Governance Plan (NeGP) for transforming Police into an IT-based force and to improve the delivery of citizen-centric services. The project...
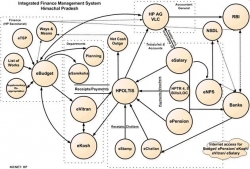
HimKosh: Integrated Finance Management System
Financial System of a country is the nerve centre of its economy, wherefrom growth is channelized in each part of the economy. With ever increasing transactions arising out of G2G, G2C, G2B and G2E services, suitable management of the financial systems has assumed paramount importance. HimKosh...
Online Filing of Entrepreneurs Memorandum (OFEM) in Manipur
Online Filing of Entrepreneurs Memorandum (OFEM) is an initiative for Department of Commerce and Industries, Government of Manipur to facilitate entrepreneurs in obtaining acknowledgement to Entrepreneurs Memorandum (EM) Part-I readily without any need of contacting the concerned General Manager of...
e-Pothi: Online Manuscripts Cataloguing System of Odisha State Museum
Odisha is known for its rich cultural heritage, monuments and palm & bamboo leaf manuscripts. The State Museum is unique in the Country, having rare & other forms of manuscripts. e-Cataloguing system (e-Pothi) has its genesis in fulfilling intellectual requirements of research scholars...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


