Articles
e-Registration by Job Seekers in Manipur
The Employment Service, Manipur came into existence in 1957 and has been working closely with its Directorate of Employment as the controlling body for administration, establishment and financial supervision, under which there are nine District Employment Exchanges, Town Employment Exchanges and...
Pre-Examinations Monitoring System for Anna University, Chennai
Anna University, a unitary type of University, offers higher education in Engineering, Technology and Allied Sciences relevant to the current and projected needs of the society in Tamil Nadu. There are about 580 affiliated engineering colleges and these colleges offer various engineering degrees...
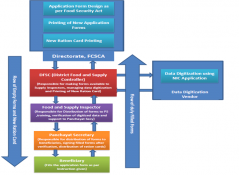
Aadhaar based Electronic Ration Card Monitoring System in Himachal Pradesh
The Public Distribution System (PDS) is the distribution of essential commodities to a large number of people through a network of Fair Price Shops (FPS). The system operates under joint responsibility of Central (procurement, storage, transportation and bulk allocation of food grains...
e-Gov Mobility Platform Services
Mobility Platform Services (MPS) is an open, comprehensive and advanced mobile application platform for smart phones and tablets, helping Government organizations of all sizes to efficiently customize the requirements, emulate and deploy on multiple platforms.
Jeevan Pramaan: Digital Life Certificate for Pensioners
In order to transform the entire ecosystem of delivery of public services through the use of ICT, Government of India has unveiled an ambitious programme called Digital India. Jeevan Pramaan (Aadhar-based Digital Life Certificate for pensioners), recently launched by Prime Minister Shri Narendra...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


