News
Honorable CM, Haryana, inaugurates portal for Online Registration of Cooperative Societies and Share Transfer for Housing Societies
Shri Manohar Lal Khattar, Honorable Chief Minister of Haryana, launched the portal for Online Registration of all types of Cooperative Societies and Share Transfer for Housing Societies (http://cooponline.rcsharyana.gov.in), at Tejli Stadium, Yamunanagar on the International Cooperative Day on 6th...
Digital India Anniversary observed at NIC State Centre, Odisha
Digital India, the flagship programme of the Government of India, was launched by Shri Narendra Modi, Honorable Prime Minister of India, on 2nd July 2015. It has three essential vision areas: Country-wide digital literacy, delivering government services digitally, and development of secure and stable...
Honorable Chief Minister, Himachal Pradesh, launches Mobile App for Drug Free Himachal
Shri Jai Ram Thakur, Honorable Chief Minister, Himachal Pradesh, launched Drug Free Himachal Mobile Application in Shimla on 30th June 2019. The Mobile App has been developed for the Narcotics Division of Himachal Pradesh Police by the NIC Himachal Pradesh Competency Centre for Mobile Application...
Two Day training conducted on eProcurement (Central Public Procurement Portal-CPPP) to IRCON, Raipur
A two-day training programme on Central Public Procurement Portal (CPPP) was organized at IRCON, Raipur from 20th to 21st June 2019 for participants from Chhattisgarh Rail Project, CEWRL –Corridor- Gevra-Pendra, Katni Yard Grade Separator Project, Katni Singrauli Doubling Project and IRCON,...
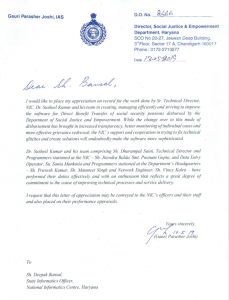
Department of Social Justice & Empowerment, Haryana, appreciates NIC Haryana team
Haryana State Government has recognized the efforts and outstanding work done by Dr. Susheel Kumar, Senior Technical Director, Shri D.P. Saini, Technical Director and other Officers of NIC Haryana for development, maintenance, implementation and providing continuous technical support for the monthly...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


