News
Workshop on e-PMS State Portal conducted at Gandhi Nagar, Gujarat on 22nd and 23rd July 2014
“ePMS, an On-line Project Management System for Gujarat tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire tracking...
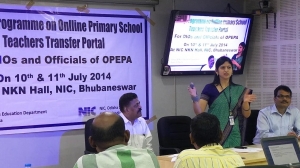
Training Programme on Online Elementary School Teachers Transfer System
Two days Training Programme on 'Online Elementary School Teachers Transfer System' for DIOs & Programmers of OPEPA of 30 Districts of Odisha was held at NKN Hall, NIC Odisha State Centre, Bhubaneswar. The training programme was inaugurated by Smt. Usha Padhee, IAS, Commissioner-cum-Secretary,...
NIC Haryana Presented e-Dashboard in North Zone symposium on Best Electoral Practices
A North Zone symposium on Best Electoral Practices was held on 25th July, 2014 at Hotel Mount View, Sector-10, Chandigarh. There were 30 participants (Chief Electoral Officers, Addl. CEOs, IGP Ranges/ SPs & District Electoral Officers) from Northern States/UTs (Punjab, Haryana, Himachal, UP, J&K,...
Inauguration of Official Website of Fisheries & Animal Resources Development (FARD) Dept, Govt. of Odisha
The official website of FARD Department, Govt. of Odisha was inaugurated by Sri Pradeep Maharathy, Hon’ble Minister, Agriculture, Fisheries and Animal Resources Development Department, Government of Odisha on 31st July,2014 in the Conference Hall of National Informatics Centre, Odisha...
Workshop-cum-Launching of C-FRO, C-Form and S-Form module under IVFRT MMP-NeGP at Paradeep, Odisha
In continuation with series of workshops for implementation of IVFRT across the State of Odisha, State Home Department in partnership with NIC organized training cum sensitization program on 15th July for Central Range at coastal port city Paradeep. A workshop and training on C-FRO, Form-C and...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


