Land Records
Training on Bhunaksha held at Jharsuguda, Odisha
Training programme on Bhunaksha software on map correction was held in the DRDA Conference hall, Jharsuguda, Odisha on 09/08/2017 for all the 5 Tahasil officials and 32 RI officials of Jharsuguda District. The training programme was organized by NIC, District, Unit, Jharsuguda. The main objective...
Roll out of online mutation (LRMS) system at Kendrapara Tahasil, Odisha
The Land Records Management System, a web enabled application for online mutation, was launched at Kendrapara Tahasil recently. It is a transaction based applications which interacts with the e-Registration application through web services. It helps the Mutation Officer (Tehsildar/Addl....
Training on BHUNAKSHA 3.0 at NIC Balangir District, Odisha
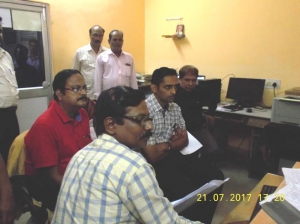
Training on Bhunaksha was organised at NIC, Balangir for all 14 Tahasils of Balangir District, Sub-division wise. The schedule was as follows: 05.07.2017 & 06.07.2017 - Balangir Sub-Division (6 Tahasils) 13.07.2017 & 14.07.2017 - ...
Training on BhuNaksha s/w for the Tahasil staffs of Ganjam District, Odisha
A two days long training programme on Bhunaksha s/w on map correction was held during 5th and 6th June’2017 in the e-Governance training centre of Collectorate, Ganjam for all the 23 Tahasil staffs of Ganjam District. The training was conducted Sub-Division wise. Ganjam has three sub-divisions...
Training program on BHUNAKSHA for Tahsil Officials at NIC District Unit, Jajpur, Odisha
A training program on BHUNAKSHA was conducted for Tahsil Officals of Jajpur district on 06.06.2017 at NIC District Centre, Jajpur, Odisha. Welcoming the participants Sri S M Satpathy, Technical Director and DIO gave a brief introduction about the BHUNAKSHA software and features available....




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


