Roll out of online mutation (LRMS) system at Kendrapara Tahasil, Odisha

The Land Records Management System, a web enabled application for online mutation, was launched at Kendrapara Tahasil recently. It is a transaction based applications which interacts with the e-Registration application through web services. It helps the Mutation Officer (Tehsildar/Addl. Tehsildar) posted at tehsil to initiate a mutation case instantly whenever there is a transaction at Registration office. Digital Signature Certificate and Biometric authentication system has been integrated in the application software.
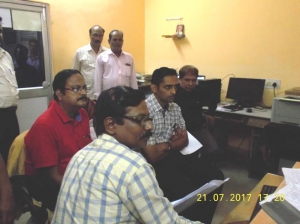
The roll out program was launched by Shri Reghu G, IAS, Collector and District Magistrate. Other dignitaries present on the occasion include Shri Dhananjaya Swain, OAS(S), ADM, Shri Kanhu Charan Dhir, OAS, Sub Collector, Dr. Hemlata Bahalia, OAS, Tahasildar, Kendrapara tahasil.
Shri Debabarta Dalar, DIO demonstrated various features of the application.
Acknowledgement letter of one mutation application was generated from the system and handed over by the Collector to the applicant on the occasion.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


