Land Records
Haryana: e-Stamping System in Property Registration launched in Haryana by Chief Minister on 2nd May, 2015 from Panchkula.
At present, State government receives stamp duty through issuance of stamp papers by Treasury (upto value of 10,000/-) and issuance of stamp duty receipt by various authorized branches of SBI (for value exceeding Rs. 10,000/-). The treasuries are required to maintain huge stock of...
Haryana: Training Session on Best Practice of NIC for Bangladesh Civil Servants
The National Centre for Good Governance (NCGG, an Autonomous Institution of Department of Personnel & Training, Government of India) , Cosy Nook, Lal Bahadur Shastri National Academy of Administration (LBSNAA), Mussoorie organized a “ Seventh Mid career Training Programme in...
Haryana bags National Award of e-Governance 2013-14
Haryana’s e-Governance project entitled, “Dynamic Integration of Property Registration, Land Records and Cadastral Maps” has received National Silver Award on e-Governance 2013-14 under the category “Incremental Innovation in Existing Project”. The award has been...
Manthan 2013 Award for HimBhoomi-Land Records Computerisation Himachal Pradesh
The HimBhoomi initiative of NIC Himachal Pradesh has been awarded the Manthan 2013 Special Mention Award under the eGovernance category in the recently held Manthan Awards 2013 (Asia Pacific South Asia) event at New Delhi. Earlier, the HimBhoomi application was selected as a Finalist. All the Finalists...
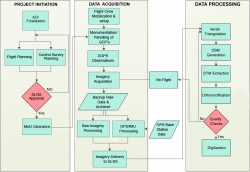
Use of Hybrid Survey Methodology and Bhu-Sarvekshan Software for Resurvey in Bihar
The Bihar state - spread over approx. 94163 sq. Km area, has an administrative setup comprising of 9 divisions, 38 districts, 101 subdivisions, 534 circles and 45,700 mauza(s) i.e. revenue villages. The very first survey of land i.e. Cadastral Survey (CS) of the state was conducted almost a century ago....




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


