Automation
e-Hospital@NIC: Simplifying Health Care Delivery
Tucked away at the southernmost tip of the Northeast, the state of Tripura has made significant contribution to public health care by pioneering e-Hospital@NIC-an integrated Hospital Management Information System (HMIS) which now runs in almost 30 major public hospitals across the country,...
LEVERAGING INTEGRATED NPR & SECC-2011 FOR ESTABLISHING NFSA 2013 DATABASE & SRDB IN HARYANA
On July 9, 2013, Government of Haryana announced implementation of National Food Security Act 2013 (NFSA 2013) from 20 August 2013 and decided to utilize provisional data of Socio Economic and Caste Survey (SECC-2011) and National Population Register (NPR-2011) on as-is-where-is basis for identification...
MALKANGIRI: e-Governance in the land of Primitive Tribes
Malkangiri district came into existence after the reorganization of Odisha state on 2nd October 1992. Covering an area of 5,791 sq. kms, almost the whole of district is covered with vast dense jungles, with tribal population comprising of primitive tribes notable among them are Bondas, Koyas,...
MANAV SAMPADA:A Green Governance tool for Human Resource and Financial Management in Himachal Pradesh
Manav Sampada is a work flow based product to eliminate paper usage in the State Government at various levels. It assists in faster yet paperless disposal of service matters, thereby improving the Carbon Credit Rating of the state. The main beneficiaries of the project are the Department of Personnel,...
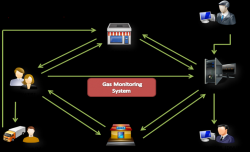
EASYGAS, KISAN: Citizen-Centric IT Innovations from Gonda, Uttar Pradesh
Achieving milestone is not an everyday business. Claiming appreciation for achievement is even tougher. The feeling goes beyond the expected elation, when endeavour, designed and perspired for common good catches peoples eyes to attain recognition. Project EASYGAS and project KISAN, the two...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


