Automation
e-TOURISM: Streamlining Tourism Using ICT
Haryana is one of the most industrialized states in India. It is also known all over the world for its culture and religious & historical events like Mahabharta. Tourists and businessmen from all over the world visit this state. To expose the tourism potential of Haryana to the world,...
Stores & Supply Management System
Information Technology based e-Governance tools have been changing the lives drastically in India. Even before that, it brings unimaginable innovative comfort to the administration in order to strengthen the public service delivery mechanism. Buzz around change management is noisier than the actual...
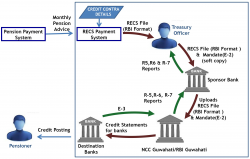
Regional Electronic Clearing Service (R-ECS) in Pension Payment System: Ensuring efficient payment to Pensioners
The payment system is one of the most important elements of a financial system and Government always looks for innovative ways of making hassle-free payments to individuals. Since electronic means of payment are both safer and more efficient, efforts are being made continuously to effect a change...
eTaal:Electronic Transaction Aggregation & Analysis Layer
To measure the impact of various e-Governance initiatives at national and state levels, NIC in collaboration with Department of Electronics and Information Technology (DeitY) has developed eTaal application. It provides an integrated view of e-Transactions taking place under various e- Governance...
ICT ENABLED IMPLEMENTATION OF FOREST RIGHTS ACT 2006 IN MAHARASHTRA
Today, Information and Communication Technology has infiltrated the remotest corners of the Earth. The Government of Maharashtra came up with an ICT based innovation to preserve the forests and the rights of those who live in these remote forest areas. Implementation of GIS and other ICT...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


