Cyber Governance
XGN - Xtended Green Node
Gujarat Pollution Control Board (GPCB) was constituted with a view to protect the environment, prevent and control pollution in the State of Gujarat. GPCB is the main beneficiary of the Xtended Green Node (XGN) software. The XGN system ensures effective monitoring and inspections of hazardous,...
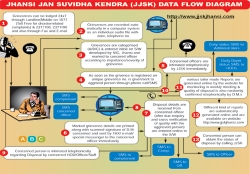
Jhansi: Leading From the Front
'Leading from the front' is synonymous with Jhansi, be it the First Freedom Struggle of India or the modern day ICT based Governance, Jhansi has been the torch bearer with earnest dedication. Centuries have moved from twentieth to twenty first but the will to provide good governance...
Manipur: Online Tenders for PMGSY through e-Procurement System
Procurement delays, unfair bidding practices, opaqueness in government processes, etc. have become things of the past with the deployment of Government e-Procurement System of NIC (GePNIC) in Manipur. The system provides transparency in the tendering process, reduces time for procurement,...
Ganjam: Pioneer in e-Governance
Ganjam district is named after the Old Township and European fort.The name Ganjam comes from the word Gan-i-aam which means Granary of the World. It is spreading over the geographical area of 8070.60 square km. in Odissa.There are 22 blocks, 475 Grampanchayats, 18 Urban Local bodies, 3229...
Commonwealth Express Train - An exposition on wheels
In the past Railways has successfully launched exhibition trains like Azaadi Express, Red Ribbon Express and National Science Express for highlighting Indian Independence, AIDS awareness and Science and Technology respectively. With Commonwealth games being hosted in India, Ministry of Railways...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


