Cyber Governance
Online Job Application System for Government of Gujarat
Those who are looking for the jobs in Gujarat State government or thinking of making careers along with the various Gujarat Government departments, they can now apply through Online Job Application System.The vision of this online system is to devise an Information and Communication Technology (ICT)...
e-College*Suite: Integrated e-Governance solution for College Campus from NIC
In terms of public governance, India has been a laggard in the utilisation of ICT. There are several reasons for this. One is the monopolistic nature of public governance. It is the customer, in this case the "aam aadmi", who has to like or lump whatever is offered by the public institution....
Eucalyptus Cloud to Remotely Provision e-Governance Applications
Cloud computing can be defined as on-demand, scalable and elastic web services on public or private fabric consisting any of grid, cluster, virtual machines and physical machines. Ensuring high reliability, scalability, high availability of citizen centric e-Governance services is very important. Cloud...
Dholpur: ICT Shines on the Eastern Gateway of Rajasthan
Situated in the eastern part of Rajasthan bordering Uttar Pradesh and Madhya Pradesh, Dholpur earlier called Dhavalpur, was carved out of Bharatpur in 1982. It is famous for its sandstone and ravines which are part of Chambal legacy. The famous Dholpur House (UPSC HQ), President House and...
Web Ratna Awards
e-Governance has received a tremendous boost in India and that gave National Informatics Centre, the inspiration to institute the Web Ratna Awards, an initiative to acknowledge the exemplary initiatives in e-Governance using the medium of World Wide Web.




 Subscribe
Subscribe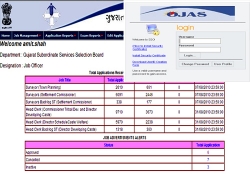




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


