Cyber Governance
ONLINE SERVICES OF DEPARTMENT OF COMMERCIAL TAXES, GOA
In order to ensure high transparency and productivity in the Department of Commercial Taxes, NIC, Goa started implementation of the VATSoft software in May 2008. Over the years, the software has been enriched by incorporating all the tax types to facilitate the Department of Commercial...
AUTOMATION OF COMMERCIAL TAX DEPARTMENT, UTTARAKHAND
The Commercial Tax Department of Uttarakhand is one of the major contributors to the state revenue. It mainly interfaces with business community and is responsible for administering value added tax (VAT), central sales tax (CST), and State Tax on entry of goods into the local market. Its functioning...
ICT in Public Distribution System
The primary policy objective of the Department of Food & Public Distribution (DoF&PD) is to ensure food security for the country through timely and efficient procurement and distribution of essential commodities across the country.This involves procurement of various food grains, building...
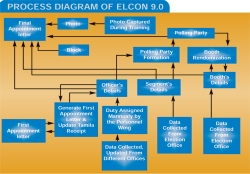
ELECON 9.0: Managing Assembly Elections in Bihar
Polling party formation, deployment of patrolling personnel, tagging of booths with the polling party, Electronic Voting Machines (EVM) randomization, vehicle allotment to the parties - all through random number techniques as per Election Commission of India (ECI) guidelines were made possible...
IMMIGRATION, VISA, FOREIGNERS' REGISTRATION AND TRACKING
The entire IVFRT system envisages the information capture from Visa applicants' details till their exit from India and utilizes these sets of information for intelligence decision making at every stage. This system would facilitate information exchange between MHA, MEA and other agencies such...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


