Cyber Governance
CSI-NIHILENT E-GOVERNANCE AWARDS 2012-13
.CSI Nihilent e-Governance Awards have been instituted to acknowledge the exemplary initiatives/projects/services in the realm of e-Governance. Running into its second decade, the award is a golden yardstick for evaluating the mileage of various e-Governance initiatives running in the country. Alike previous...
SAMAY SUDHINI SEVA- Online Monitoring of Time Bound Services
UT Administration of Daman & Diu and Dadra & Nagar Haveli in collaboration with National Informatics Centre have implemented an online web based Monitoring System for time bound services known as Samay Sudhini Seva.
NEET-UG -National Eligibility cum Entrance Test for Under Graduates
The Medical Council of India and the Dental Council of India have notified that the Central Board of Secondary Education (CBSE) shall be the organization to conduct the National Eligibility cum Entrance Test for admission to MBBS and BDS courses. CBSE, in technical collaboration with NIC, has...
SEHORE: Heralding a Paradigm Shift in e-Governance Regime
Sehore lies in the foothills of Vindhyachal Range surrounded by of Malwa region in Madhya Pradesh. It is about 39 Kms away from the state capital Bhopal towards south and spread across 6578 Sq. Kms. Shaiva, Shakta, Jain, Vaishnav, Budhists and Nath priests made Sehore a significant seat of their...
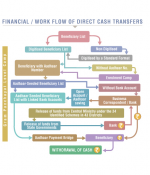
MIS ON DIRECT BENEFIT TRANSFER (DBT)
The machinery of all Government Departments now depends on ICT to transform Government business and services to meet people expectations for better services. Every department is putting in its best efforts to build capability in government to meet peoples need and deliver improved services and...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


