Cyber Governance
PAKUR: Empowering Citizens through e-Governance
Situated in the north-eastern corner, Pakur is one of the twenty four districts of the Jharkhand state and is topographically divided into three distinct regions - hilly, rolling and alluvial. The district is predominantly agricultural based and the main occupation of the people is cultivation....
LEVERAGING INTEGRATED NPR & SECC-2011 FOR ESTABLISHING NFSA 2013 DATABASE & SRDB IN HARYANA
On July 9, 2013, Government of Haryana announced implementation of National Food Security Act 2013 (NFSA 2013) from 20 August 2013 and decided to utilize provisional data of Socio Economic and Caste Survey (SECC-2011) and National Population Register (NPR-2011) on as-is-where-is basis for identification...
eTaal:Electronic Transaction Aggregation & Analysis Layer
To measure the impact of various e-Governance initiatives at national and state levels, NIC in collaboration with Department of Electronics and Information Technology (DeitY) has developed eTaal application. It provides an integrated view of e-Transactions taking place under various e- Governance...
MANAV SAMPADA:A Green Governance tool for Human Resource and Financial Management in Himachal Pradesh
Manav Sampada is a work flow based product to eliminate paper usage in the State Government at various levels. It assists in faster yet paperless disposal of service matters, thereby improving the Carbon Credit Rating of the state. The main beneficiaries of the project are the Department of Personnel,...
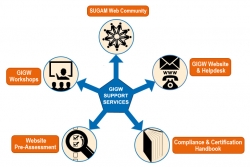
POWERING GIGW COMPLIANCE
In the last decade or so, India has metaphorically witnessed a lot of water surge & not just meekly flow under the bridge. Technology has played an increasingly prominent role as enabler and leveller. Enabler- Technology continues to bring a flood of opportunities to lead lives very differently...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


