Cyber Governance
ICT Initiatives in the Office of Chief Secretary, Haryana
The Chief Secretary Office (CSO) is the Principal Executive Office of the Government of Haryana. The Chief Secretary Haryana also holds the charge of General Administration, Personnel, Training, Vigilance, and Administrative Reforms Departments. The CSO monitors and coordinates the work pertaining...
Faridabad: ICT in the Medical & Educational Hub of Haryana
Faridabad was founded in 1607 A.D. by Shaikh Farid, the treasurer of Jahangir, with the objective of protecting the highway which passed through the town. It came on the map of Haryana on 15th August, 1979 as the 12th district of the state. Situated about 25 Kms. from Delhi, it is a part of...
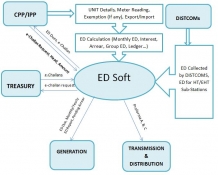
EDSoft: Online Collection and Monitoring of Electricity Duty in Odisha
The EDSoft system radically enhances collection of electricity duty in the state of Odisha. The system builds consumer database, calculates Electricity Duty, facilitates e-payment, monitors arrear, exemption, export grants etc. ensuring transparency at all levels.
MANDI: Taking ICT to the Masses
Mandi, one of the twelve districts of Himachal Pradesh, is the second largest district in terms of administrative strength. Mandi is also known as Chhoti Kashi, thanks to so many temples in the town. Due to its varied altitude, there are some places in the district where the climate is quite...
e I T I s : Standardizing Industrial Training Institutes in Punjab
Due to ever increasing demand for skilled manpower, large scale establishment of the Industrial Training Institutes (ITIs) is taking place both in public as well as in private sectors. At the same time, there is a need to regularly monitor the infrastructure, results, faculty, trainees etc. of...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


