Data Centre
Educating & Empowering Masses through IT
In an exclusive interview session with Informatics, Sh. Chandra Prakash, IAS Principal Secretary, IT & Electronics, GoUP talks about how the implementation of e-Governance initiatives is fast changing the image of Uttar Pradesh from an IT laggard state to an IT happening state.
Network Access Control and End Point Compliance
Cybercrime continues to rise, with the primary aim to compromise an organisations information that will make a profit for the perpetrators. To avoid the unwelcome publicity provoked by IT failures, securing the network is more important today than ever before. It's also tougher to achieve, as today's...
Purnea District: Cementing ICT for Masses
Constituted in the year 1813 the Purnea District comprises the eastern most part of the alluvial North Bihar plain. The name district was derived from the lotus flower, which was found in abundance in the past in the canal of Kosi and Mahananda rivers. Situated along the border of West Bengal &...
West Singhbhum - Winner in Implementing ICT Projects
Adorned by hills and plateaus, spreading natural splendor with sparkling rivers amidst dense forests, harboring variety of flora and fauna, West Singhbhum, situated in the southern part of Jharkhand state. The largest district of the state, came into being in 1990, when the erstwhile Singhbhum district...
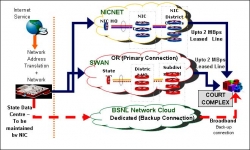
e-Courts Mission Mode Project: The Journey so Far
ICT enablement of judiciary is being pursued vigorously across the world. In India, ICT enablement of higher judiciary started in early nineties, covering the Supreme Court and all the 21 High Courts. Today, we have reached a stage where deployment of ICT in Supreme Court and the High Courts has reached...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


