Data Centre
Assam -Weaving ICT Dreams into Reality
Assam - popularly called the land of red river and blue hills, famous for its tea and one-horned rhinoceros, dominated by the mighty river Brahmaputra, is the gateway to the northeastern India. The state has a large number of tribes each unique in it's tradition, culture, dresses and exotic way...
Andhra Pradesh: A Right Place for Technology Breeding
Andhra Pradesh also known as the Rice Bowl of India is the fourth largest state in India. The state is not only famous for its rich culture and heritage but also a favourite place for tourists worldwide for its spellbound beaches. Of late the state has received lots of accolades in the global platform...
Hazaribag - Harnessing ICT for Good Governance
Hazaribag- literally meaning City of Thousand Gardens, is situated at 2019 ft above the sea level in the North Chotanagpur Plateau. Congenial salubrious climate, abundant flora, fauna, wildlife sanctuary, lakes and hills have attracted tourists to this place since long and is also considered as a health...
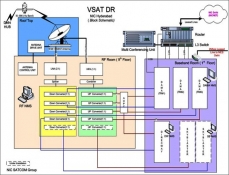
Data Center Operations and Management
Data Centre management is a pretty complex task and needs a multidisciplinary, highly skilled team to effectively & efficiently manage it. Data Centre management requires additional IT attention and resources. The consequent write up is all about the management infrastructure involved in managing...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


