Data Centre
SSL VPN: A Technology Overview
In the world of distributed computing, corporate applications are hosted in data centers located in multiple locations and are accessed by many users from various locations. To provide secure access to such network resources, technocrats have designed Secure Socket Layer Virtual Private Network (SSL...
Hands free Computing by Integrating Speech Recognisation
Voice reorganization and text to speech system is becoming a powerful tool to provide the services through ICT for the physically handicapped people. While entering to ATM counters and just after swapping the ATM card in the reader, a greeting voice as well as guiding instruction can be heard in almost...
Interview with Sh. S.R Rao, Additional Secretary DIT
National e-Governance Plan (NeGP) is one of the landmark programmes of the department. It has been operational for some time now. How is it shaping up the e-Governance landscape in the country?
EVCS over NICNET by Cabinet Secretary- Moving a Step Ahead in e-Governance
The Government is according high priority to various e-governance initiatives. For improving e-governance, communication is a key ingredient and forms the basis of instructions. The Cabinet Secretariat invited National Informatics Centre, DIT, GOI, to operationalise the Executive Video Conferencing System...
MIS for Indira Gandhi National Old Age Pension Scheme
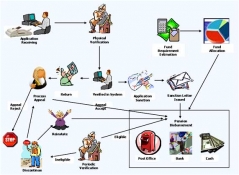
Indira Gandhi National Old Age Pension Scheme is introduced by the Ministry of Rural Development, Govt. of India to provide a steady monetary assistance for all man and women of India above the age of 65 years of age and below poverty line. In addition to the existing IGNOAPS scheme, the Govt. Of India...




 Subscribe
Subscribe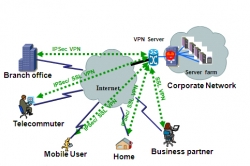


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


