e-Services
eCabinet - Automate Cabinet meetings in paper free and virtual mode
eCabinet/ eMantrimandal is a powerful software portal for State governments to conduct Cabinet meetings electronically and online mode. Developed by NIC, it maximizes usage of technology in meetings and reduces paper use. eCabinet automates work flow activities of meetings; before, during and after....
Digital Village Harisal - Striding with the Digital Way of Tribal Development
Technology enablement activities took a big leap at Harisal village from March 2016. Since then, several organizations have partnered in initiatives to address gaps in the progressive path. Many more joined the path of transformation from mere digital technologies to smart technologies....
National Cloud NIC - Ensuring seamless & uninterrupted service during COVID19 crisis
Covid-19 pandemic has disrupted normal life and citizen services globally. The Indian IT landscape has not been left untouched by this global phenomenon and this has altered IT functioning. The novel coronavirus has accelerated the demand for applications and services which enable the Government,...
Video Conferencing - NIC is providing Videoconferencing facility from 2100+ Videoconferencing studios over NICNET spread across the country
Video Conferencing services of NIC are secure and have the largest coverage in the government sector across the country. NIC is providing Videoconferencing facility from 2100+ Videoconferencing studios over NICNET spread across the country spanning State Capitals, Union Territories and Union Ministries, Departments...
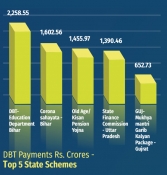
Direct Benefit Transfer - Supporting the financial Institution of the government during the crisis of COVID-19
Direct Benefit Transfer (DBT) plays an important role during the crisis times to provide sustenance to the highly effected population such as farmers, daily wagers, migrant labours etc. by transferring cash benefits directly to their bank accounts as well as delivering in-kind benefits such as...




 Subscribe
Subscribe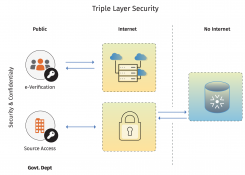




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


