e-Services
Integrated ShalaDarpan - Decision Support System for Schools Monitoring & Management
ShalaDarpan is a unique idea to provide an end-to-end solution to the Education department for effective monitoring and management of all Government Schools. System facilitates decision support, Planning (School Open/ Upgrade/ Merge/ Close), School operations (Admissions, Promotions,...
Patna District - Combating Covid-19 pandemic situations with efficient ICT interventions and Management
Patna became the first district to implement the e-Pass system of NIC in Bihar. With the application, a web portal was also created to enable citizens apply for e-Pass with much ease. The system has benefitted many who were stranded due to medical or other emergency reasons at various...
Prayas - Pursuing Excellence in Governance
Prayas provides powerful visualizations, robust analytics and actionable insights to enable Government to align well with key policy makers and program executioners. This platform with consolidated view of 100+ schemes and 600+ KPIs paves the path for better Governance. The platform today visualizes the...
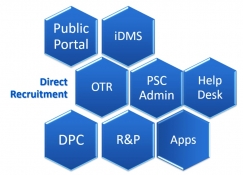
PSC-Soft Public Service Commission Software for Transformation
The PSC-Soft provides an integrated solution for the core functions of any State Public Service Commission with focus on providing user friendly interface for applicants with one-time registration facility. It is highlighted by the fact that during initial implementation stage in HPPSC, the...
eAbgari - End-to-End Solution for Comprehensive Transformation of State Excise
eAbgari has been the single most transformational factor in state excise sector and has greatly increased the department's enforcement and regulatory capabilities through ICT driven process reengineering. Seamlessly integrating a wide array of innovative technologies - the web, QR codes,...




 Subscribe
Subscribe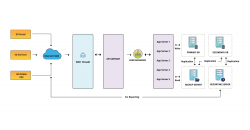




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


