e-Services
eOffice - A digital work place solution for Working From Home during COVID-19 pandemic
During the period of lockdown necessitated by COVID-19, work from home became the new mantra in public as well as the private sector. Governments whether Central or State, have traditionally followed a paper-based office. While the seeds of switchover to a less paper office were sown much earlier,...
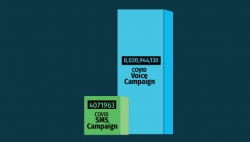
Messaging Services of NIC
During COVID pandemic, SMS service has seen a growth of almost 24% and has played a critical role in communicating with citizens
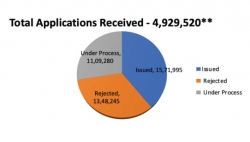
COVID-19 e-Pass - A ServicePlus Success Story
The Covid-19 menace was spreading vigorously in the country. On 24th March 2020, honourable Prime Minister of India declared a nationwide lockdown for three weeks. It was part of a preventive measure to tackle the pandemic. Lockdown limited the movement of the entire population of the country, but...
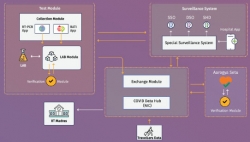
Integrated Core COVID-19 Management Framework - Ensuring availability of data across systems for better management of COVID-19 crisis
Corona virus pandemic has spread across the world at a fast pace disrupting life in unprecedented ways. Government of India has taken multiple measures like nation-wide lockdown, identification of hotspots/ containment zones, isolating patients and suspects, contact tracing, surveillance besides...
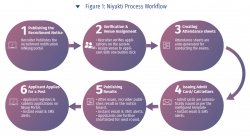
Niyukti - A one stop recruitment solution for the Government of Assam offered as a service
Since its inception in the year 2017, Niyukti has quickly evolved as a widely used recruitment solution in Assam Government. Its USP lies in the fact that it is offered as a service to the recruiting agencies, thereby allowing them to quickly onboard with a recruitment process in no time. Already...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


