G2C
ICT in Public Distribution System
The primary policy objective of the Department of Food & Public Distribution (DoF&PD) is to ensure food security for the country through timely and efficient procurement and distribution of essential commodities across the country.This involves procurement of various food grains, building...
e-Abhijoga :Chief Minister's Online Grievance Redressal Portal to reach the unreached
Government of Odisha has taken up on priority basis the e-Governance initiative to bring transparency in Public Administration and Grievance Redressal. Thus the State Government and National Informatics Centre (NIC) have jointly committed to implement e-Abhijoga Grievance Redressal Portal...
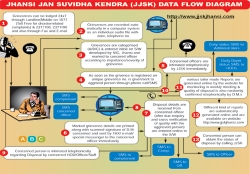
Jhansi: Leading From the Front
'Leading from the front' is synonymous with Jhansi, be it the First Freedom Struggle of India or the modern day ICT based Governance, Jhansi has been the torch bearer with earnest dedication. Centuries have moved from twentieth to twenty first but the will to provide good governance...
Tirunelveli: A pioneer District in e-Governance implementation
Tirunelveli District is one of the oldest and biggest districts in Tamil Nadu State with 11 Taluks and 19 Developmental Blocks as its administrative units.The District has a large number of educational institutions, hence, the title "Oxford of South India". In spite of its traditional...
Ganjam: Pioneer in e-Governance
Ganjam district is named after the Old Township and European fort.The name Ganjam comes from the word Gan-i-aam which means Granary of the World. It is spreading over the geographical area of 8070.60 square km. in Odissa.There are 22 blocks, 475 Grampanchayats, 18 Urban Local bodies, 3229...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


