G2C
e-CMRF: Chief Minister's Relief Fund Automation at Odisha
e-CMRF is a web based application system has been implemented for the automation of Receipts & Issue of assistance under Chief Minister's Relief Fund (CMRF),to bring transparency & accountability at every level and promote timely assistance to the needy citizen.
National Consumer Call Preference Registry (NCCPR)
NCCPR aims to curb Unsolicited Commercial Communications i.e. any message, through voice or SMS, using telecommunications service, which is transmitted for the purpose of informing about, or soliciting or promoting any commercial product or service, which a subscriber opts not to receive, but does not...
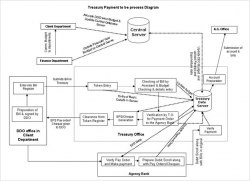
Electronic Payment System in Haryana
Two years back the treasuries were working on an archaic system which involved stamping 'Pay Order' on the bills presented at the treasury which was then returned to DDO to be presented at the bank for payment. This resulted in problems like wrong payments, unauthorized alterations in amount,...
Unique eProcurement initiative of Mahanadi Coalfields Limited
Unique eProcurement initiative of Mahanadi Coalfields Limited-A close interaction with Sh. A.N Sahay, Chairman-cum-MD, MCL.
Purulia - Using ICT for Citizen Centric Services
Purulia-The westernmost district of West Bengal state has all-India significance because of its tropical location, its shape as well as function like a funnel. It funnels not only the tropical monsoon current from the Bay to the subtropical parts of north-west India, but also acts as a gateway between...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


