G2C
Online Job Application System for Government of Gujarat
Those who are looking for the jobs in Gujarat State government or thinking of making careers along with the various Gujarat Government departments, they can now apply through Online Job Application System.The vision of this online system is to devise an Information and Communication Technology (ICT)...
Amravati: Using ICT to Reach the Poor Directly
Amravati is also known as Amrawati or Amraoti. It is believed to be the city of Lord Indra, the king of gods. The city boasts of historical temples of goddess Amba, Lord Shri Krishna and Shri Venkateshwara. But today the district is known for its robust ICT implementations, advanced communication technologies...
Jammu & Kashmir: Embraces ICT for e-Governance
J&K State comprises of three geographical regions, namely Jammu, the Kashmir valley and Ladakh. Administratively, it is divided into two divisions namely Jammu and Kashmir. Jammu is the winter capital and Srinagar is the summer capital. J&K has 22 Districts of which 8 are newly created....
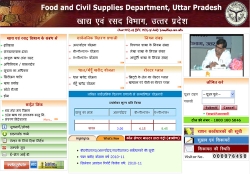
Uttar Pradesh:Focusing on Rural e-Governance
Uttar Pradesh is the most populous state accounting for about 17 percent of the country's population. It is the fourth largest state in terms of size covering nearly 9 percent of the country's geographical area. With 72 districts and nearly 1 lakh villages the state is also larger...
Dholpur: ICT Shines on the Eastern Gateway of Rajasthan
Situated in the eastern part of Rajasthan bordering Uttar Pradesh and Madhya Pradesh, Dholpur earlier called Dhavalpur, was carved out of Bharatpur in 1982. It is famous for its sandstone and ravines which are part of Chambal legacy. The famous Dholpur House (UPSC HQ), President House and...




 Subscribe
Subscribe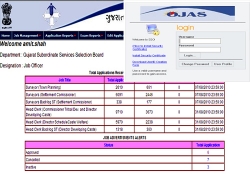




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


