Articles
NICSI Celebrates its Silver
National Informatics Centre Services Inc (NICSI) celebrated its Silver Jubilee on 28 Jan 2021 at a formal event at Vigyan Bhawan, Delhi.
NIC celebrates AI Day, 2021
Artificial Intelligence (AI) Day was celebrated by NIC on the 25th January 2021. Hosted at NIC HQ, the event witnessed the participation of NIC officials from across the nation through video conferencing.
Karnataka State - Architecting digital solutions and delivering key ICT services to the Government
NIC Karnataka State Centre has been instrumental in designing, developing and implementing e-Governance solutions, which resulted in digital transformation in the State at all levels and has helped in achieving transparency and efficiency in the delivery of the citizen centric services....
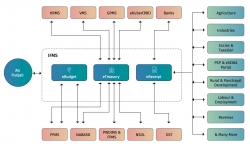
IFMS Punjab - The Next Gen Integrated Financial Management System
With release of Revised Estimate (RE) for Financial Year 2020- 21, Government of Punjab has shifted to next-gen Integrated Financial Management System (IFMS) developed by NIC Punjab. In addition to usual features of an IFMS like planning, budgeting, receipt, expenditure, bill and payment...
AABHAR - The Digital integrated pension system with mobile app eKoshLite (Pension Corner)
AABHAR,the web enabled pension portal is a fully integrated end-to-end processbased solution facilitating all processes digitally without any physical file movement. The finance department has made necessary amendments in finance rules and procedures accordingly and adopted process re-engineering....




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

