Articles
Prayas - Pursuing Excellence in Governance
Prayas provides powerful visualizations, robust analytics and actionable insights to enable Government to align well with key policy makers and program executioners. This platform with consolidated view of 100+ schemes and 600+ KPIs paves the path for better Governance. The platform today visualizes the...
Indian Customs EDI Systems - Taking Ease of Doing Business to greater heights
A significant step was taken in the year 2009, to transform the then existing ICES Application to a uniform and centralized software which culminated successfully with the launch of ICES 1.5. Thus the de-centralized application gave way to a robust central server based application. The many features of...
Securing Mobile Applications - Best practices in Mobile Application Development
Android, iOS and hybrid apps are vulnerable to a range of threats, and businesses need to be protected from the risk associated with running mobile apps in an unprotected environment. This becomes more important when it is about the Apps for government. Platform-specific security best practices...
Load Testing as a Service - Self Service model for application load testing
Modern day G2C services expect very high concurrency in production. In order to ensure that the quality of service matches the expectations of end user, it is vital to perform a thorough load testing of application prior to its release. Load testing of such application requires considerable investment...
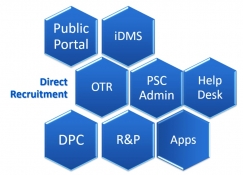
PSC-Soft Public Service Commission Software for Transformation
The PSC-Soft provides an integrated solution for the core functions of any State Public Service Commission with focus on providing user friendly interface for applicants with one-time registration facility. It is highlighted by the fact that during initial implementation stage in HPPSC, the...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

